Logging Policy Template - Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Cis assembled a working group of policy experts to develop the information security policy templates.
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,.
Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target.
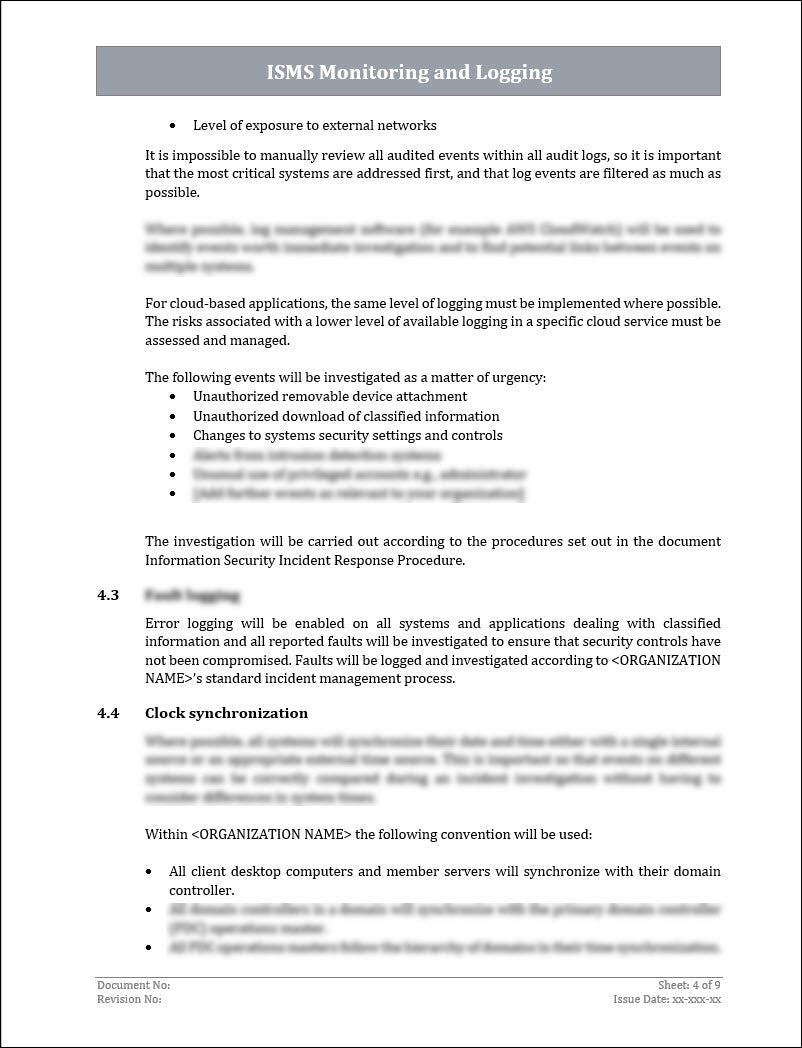
ISO 270012022 Monitoring and Logging Policy Template ISO Templates
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Cis assembled a working group of policy experts to develop the information security policy templates.
Log Management Policy Template Printable Word Searches
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,.
The Ultimate ISO 27001 Logging and Monitoring Policy Template
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Cis assembled a working group of policy experts to develop the information security policy templates.
ISO 27001 ISMS Logging And Monitoring Policy Template ISO Templates
Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target.
Audit Log Management Policy Template for CIS Control 8
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,.
Logging and Monitoring IT Standard Templates at
This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates.
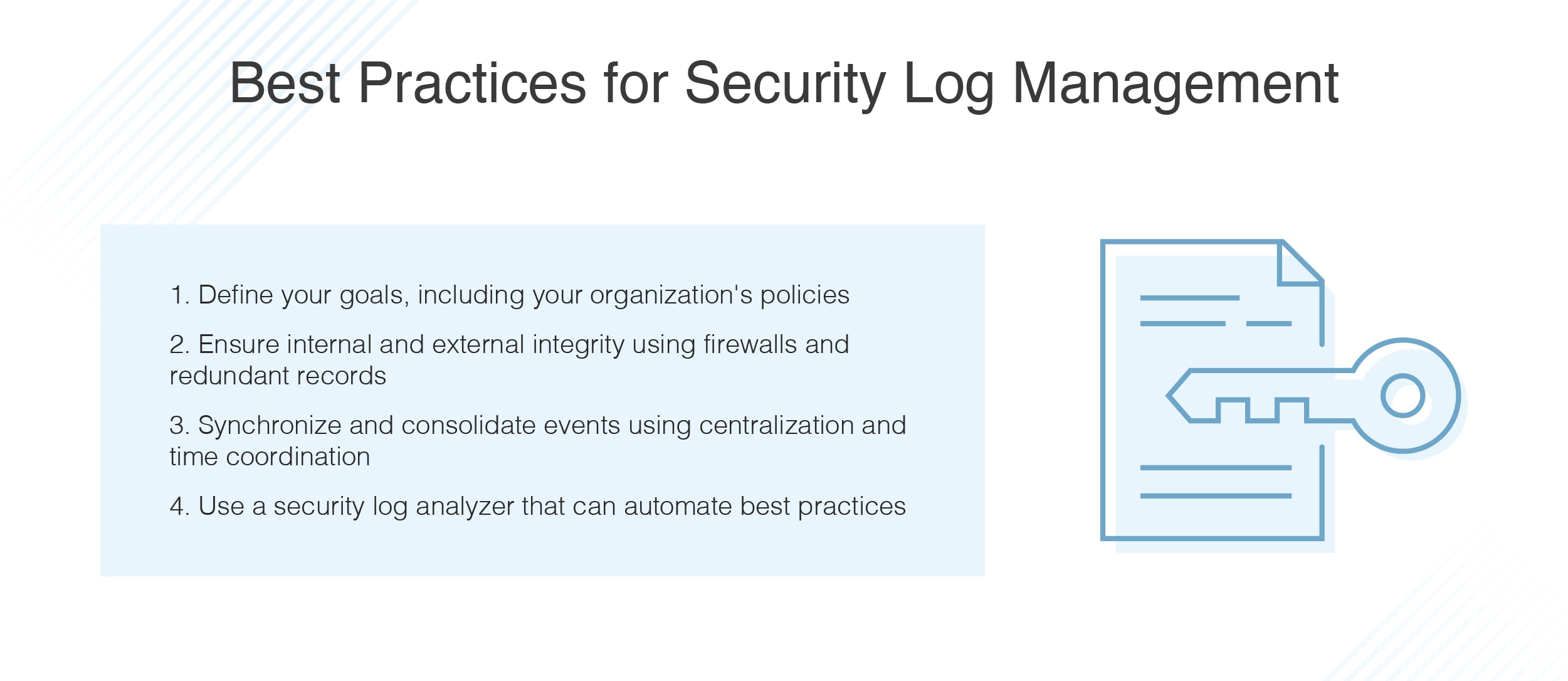
Security Log Best Practices for Logging and Management DNSstuff
This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates.
What is log monitoring? The best practices, use cases and benefits.
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. Cis assembled a working group of policy experts to develop the information security policy templates. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,.
ISO 270012022 Monitoring and Logging Policy Template ISO Templates
Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Cis assembled a working group of policy experts to develop the information security policy templates.
The Ultimate ISO 27001 Logging and Monitoring Policy Template
Cis assembled a working group of policy experts to develop the information security policy templates. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target. This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,.
Cis Assembled A Working Group Of Policy Experts To Develop The Information Security Policy Templates.
This policy template guides personnel in effectively managing the collection, storage, analysis, and retention of logs,. Due to poor or nonexistent log analysis processes, attackers sometimes control victim machines for months or years without anyone in the target.